Access Group Guide
Campus Data's access groups are a set of tools to help you effectively share data items and to manage data access requests. Access groups are fully functional ActiveDirectory groups allowing you to include any user in the campus directory. Groups are created and managed at the team level by your team's publishers, and they integrate tightly with the configuration of data items. Access groups give you precise control over who can access your items. Additionally, you can configure an access request process that will automatically add approved users to a specific group.
Managing Groups
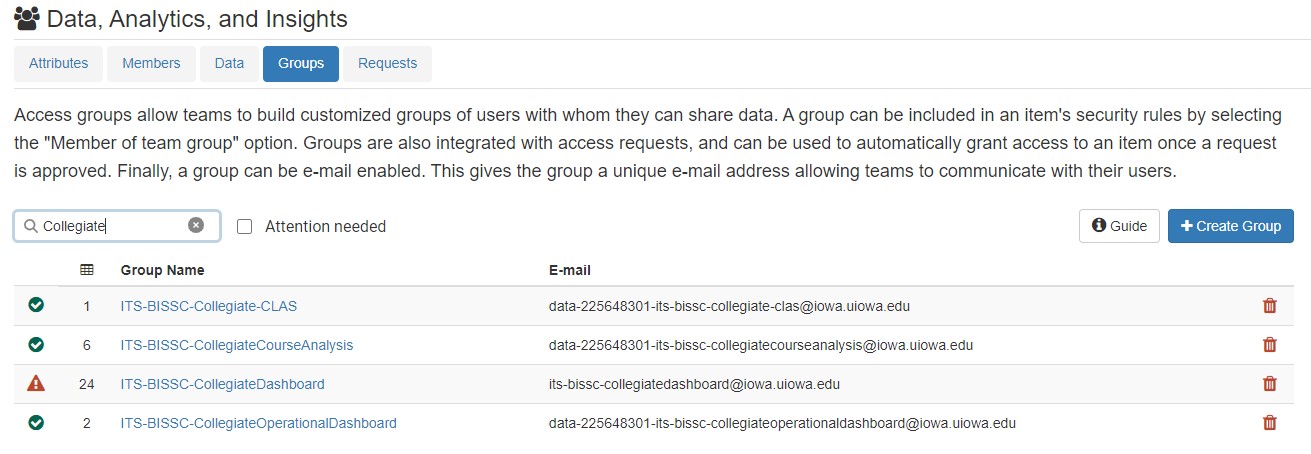
Start working with access groups by clicking "Teams" in the main menu and then selecting the team for whom you wish to build a group. Finally, click the "Groups" option in the menu directly below the team name. This screen is the primary starting point, which will allow you to create and manage your groups. It allows you to create a new group, lists the team's existing groups, and allows you to delete a group.
This screen also highlights team groups that have Access Workflow configuration issues. Groups with a green check have consistent Access Workflow configured across all items where that group is used. Groups with a red icon have one or more items where the Access Workflow does NOT match other secured items. Click the red/green icon to go directly to the Group Usage page where you can fix the misconfiguration.
Creating an Access Group
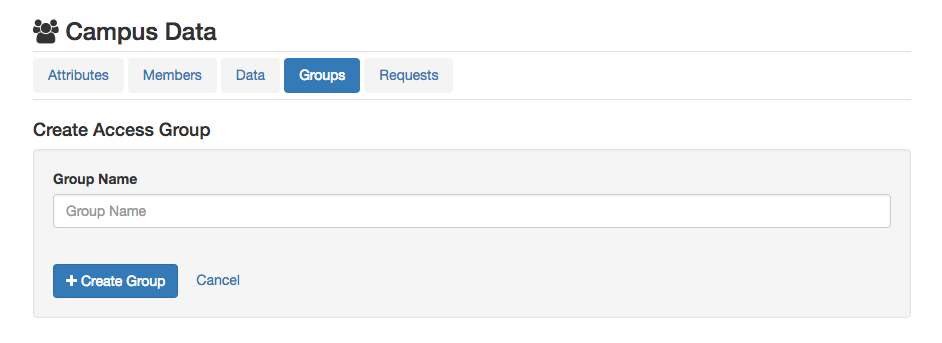
To create a group, select the "Create Group" button. When choosing a group name, try to be descriptive yet concise. Include related team or application names if possible. As an example, for a group of MAUI developers, you might choose maui-developers. Or if HR has a sub-team for compliance efforts, they might choose hr-compliance-admins. Group names must be unique within your team. To prevent collisions with other ActiveDirectory groups on campus, Campus Data will qualify the official group name such that it is unique while setting the group's display name to the value you specify. As a result, Campus Data users will see the MAUI group above as maui-developers however the official AD name will be of the form data-3423423-maui-developers where the number is associated with the Campus Data team.
Group Configuration
To build and configure an access group, click on the name of the group you wish to work with on the main list of groups. This will take you to the group members screen. There are four distinct screens for building and managing a group. They are Members, Usage, History, and Details. You will find a menu with these option in the upper right-hand corner of each group page. Each screen is explained below.
Group Membership
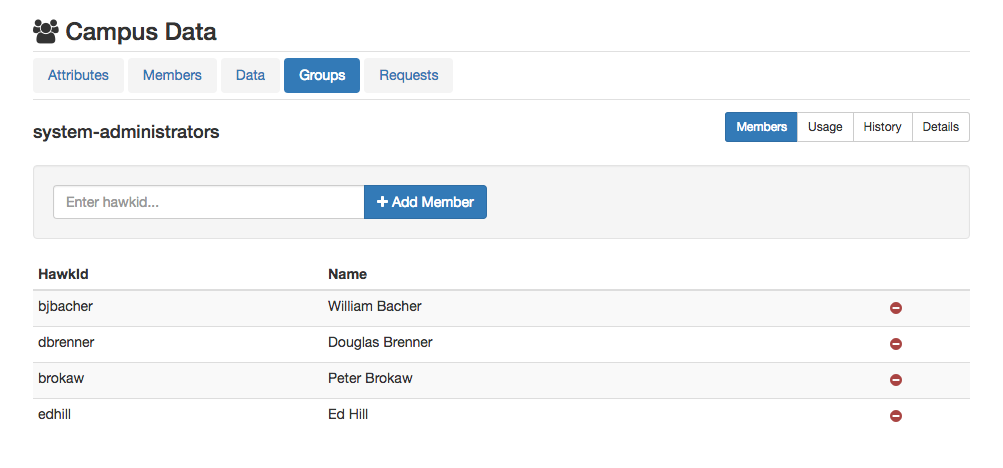
The core of every access group is its list of members. The membership screen provides the list of the current members along with controls to add new members and delete existing members. To add a member, enter a unique identifier in the input box and click "Add Member". You can use:
- HawkID
- Email Address
- UniversityID
You can look up a person's hawkid/email address in the Campus Directory.
Group Usage
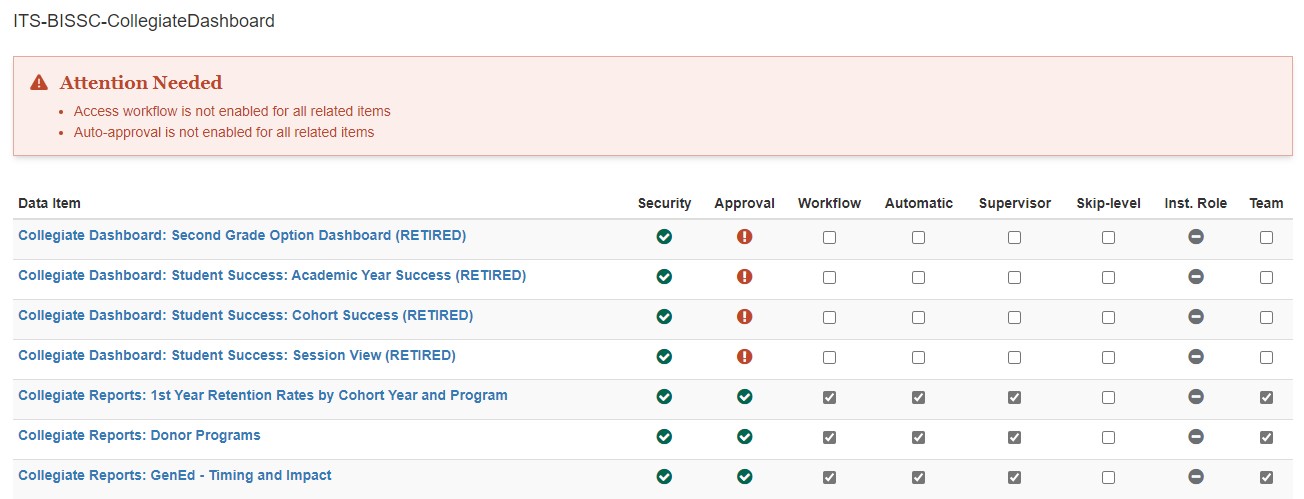
The usage screen provides an overview of all the data items that use the group in either their security or access configuration. This will quickly show you how the group is being used and expose potential problems with item configuration. For example, if an item is configured to add new users to the group but the group is not used in the item's security, the usage screen will flag that as an error.
Errors can be corrected directly on the usage tab by clicking on the setting you want to modify.
Group History
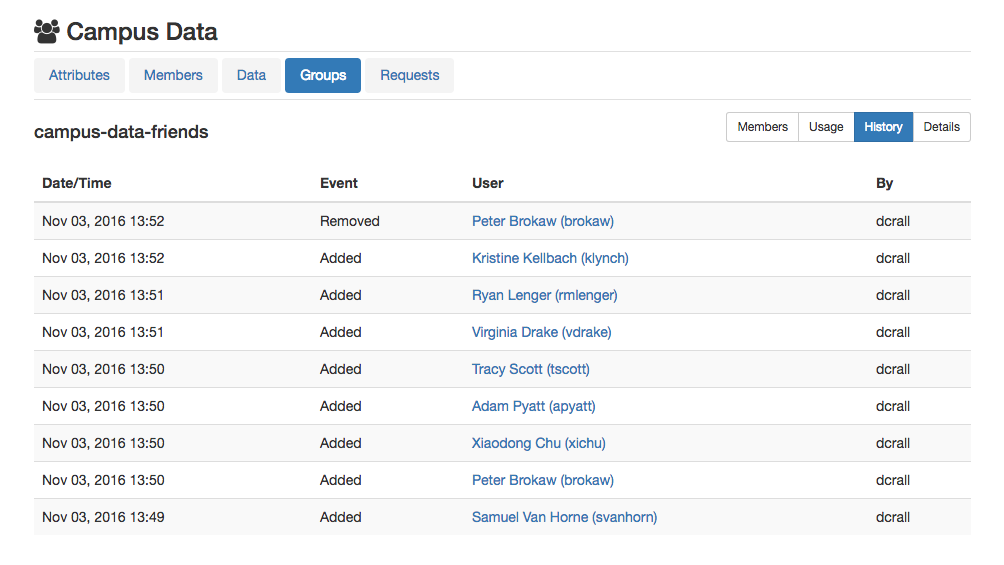
The history screen provides a log of when users are added to and removed from the group. The log specifies when the activity occurred and who triggered the action.
- Campus Data automatically removes users from team groups when they change roles or departments. This removal be listed in the history with Campus Data as the entity that made the change.
- If a user is added through Access Workflow, this addition will be listed in the history with Campus Data as the entity that made the change.
- If a user is added/removed manually, the modification will be listed with the HawkID of the person who made the manual update.
Group Details & E-mail Address
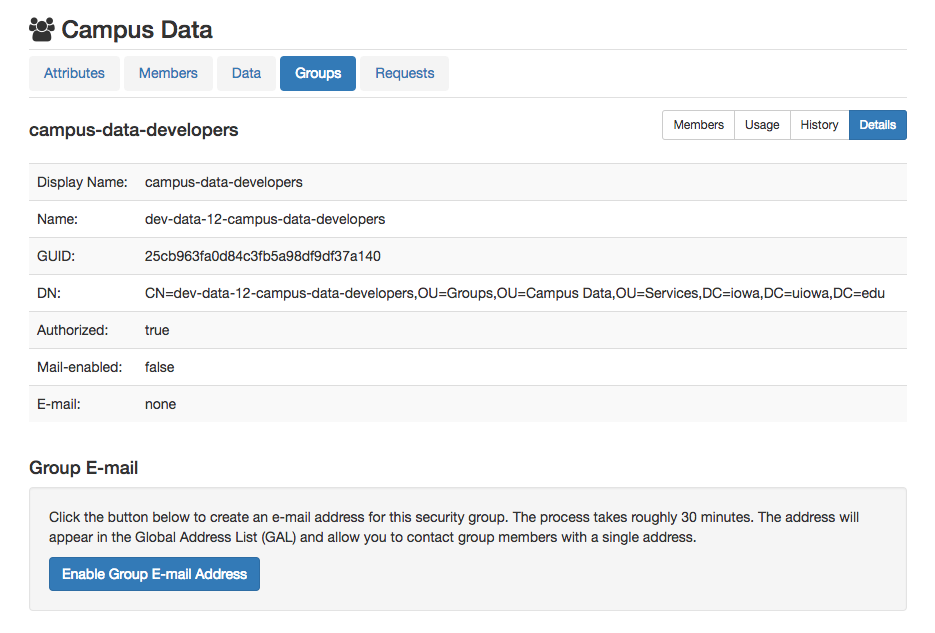
The Details screen provides low-level details about the Active Directory group. Most of the information isn't necessary to use the group, but a few key pieces of information are here that you should be aware of.
- Enable group e-mail: Activating this option will create a single e-mail address that can be used to communicate with all group members.
- Name: Immediately under the Display Name (which is what you'll see in Outlook) is the "Name" field. This will be data-[unique id]-[display name]. This is the value you need to use when updating the security on SSRS or PowerBI internal folders.
- Terms of Use: Entering Terms of Use here will require users to read and accept these terms prior to submitting a request for access via Access Workflow.
NOTE About Enabling Email: The process to create the e-mail address can take up to 30 minutes to complete. Once submitted, the Details screen reflect the fact that the request was submitted. After the address is successfully created, the group details will include the e-mail address. If the address is not available after two hours, an error message will appear. If the process fails, please contact site administrators for further assistance.
Composite Groups
Composite groups allow you to "merge" Campus Data Access Groups with Institutional Roles.
- Groups to Sync = Comma-separated list of Campus Data Access Groups to sync into the composite group
- Roles to Sync = Comma-separated list of Institutional Role KEY values to sync into the composite group (includes Members AND Administrative Delegates)
- Sync happens DAILY.
- Someone added to an institutional role on Day X should be in the composite group by noon on Day X+1.
- Likewise, someone REMOVED from an institutional role on Day X should be OUT of the composite group by noon on Day X+1.
IMPORTANT NOTE: These groups can NOT be used as the target for Access Request Workflow (see Item Access Approval below), because their membership comes exclusively from the synced groups/roles. This means people can NOT be added directly to the composite group. To enable Access Request Workflow on a data item permissioned with a composite group, make the target group one of the groups configured in the "Groups to Sync" box of the composite group.
Data Item Security Integration
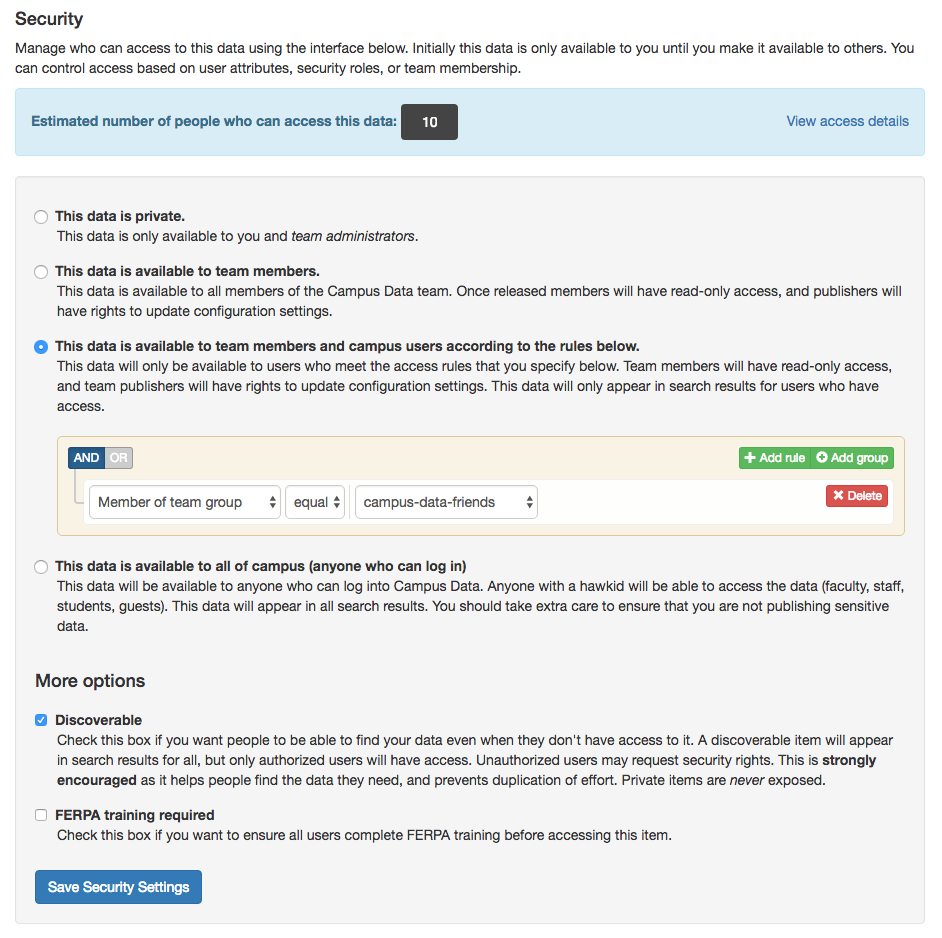
To use a group to control access to a data item, you must specify the group in the item's security configuration. Navigate to your item and select "Security" from the Settings menu. Next select the option labelled by This data is available to team members and campus users according to the rules below. After choosing this option, you will be presented with the security rule builder. In the first select menu, choose the option labelled Member of team group. This will cause your access groups to be populated in the third menu. Choose the group that should grant access to the item and save your settings.
If you want users to be able to request access to your item, you should check the Discoverable option at the bottom of the Security screen. This will cause your item to be visible in search results even if the user does not have access. Users without access will be prompted to request it.
Data Item Access Approval
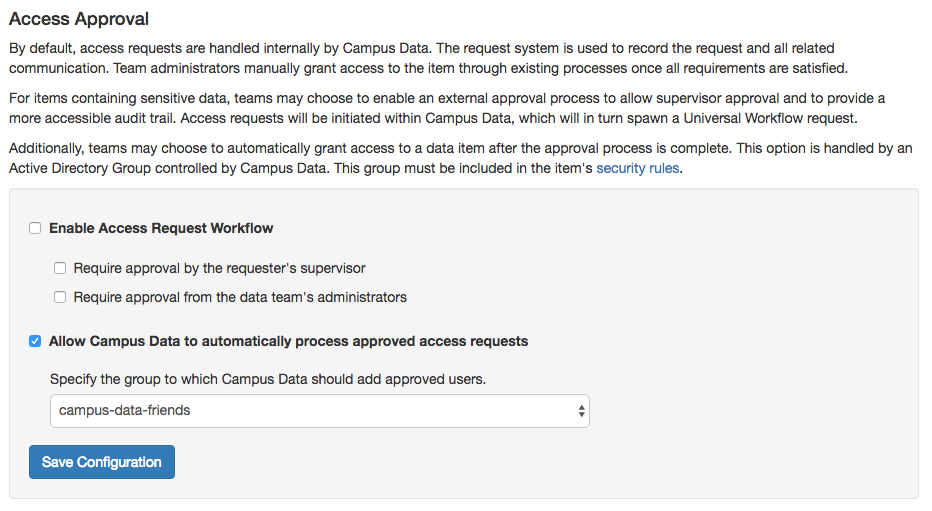
To automatically add approved users to your group, you must specify the group in the item's access approval configuration. Navigate to your item and select "Access Approval" from the Settings menu. There are two overarching options here. The first is to enable an access approval workflow. If this is selected, access requests will be created in the Universal Workflow system. Otherwise, the requests will be handled internally within Campus Data. Internal requests require approval from the data team. External requests can require either supervisor approval, data team approval, or both.
The second option, which is relevant to access groups, is the option to automatically process approved access requests. If this option is activated, you must specify the access groups to which approved users will be added. When a user successfully completes the approval process, Campus Data will be notified and that user will be added to the specified access group. The user will then be given access to the data item within 10 minutes.